Can PGP encryption be cracked
It has not been cracked. The strategies used to subvert PGP do not rely on cracking the encryption. The maths makes this an unrealistic target as the whole protocol is designed to make a brute force attempt at cracking extremely computationally demanding. However the weakness in the system lies with the keys.
How long does it take to crack PGP?
56-bit key: Less than half a day. 64-bit key: Half a year (starting today). 80-bit key: One year of brute-forcing after 30 years of tech improvement (or roughly 33 thousand years with today’s tech). 96-bit key: One year of brute-forcing after 62 years of tech improvement (or over two billion years with today’s tech).
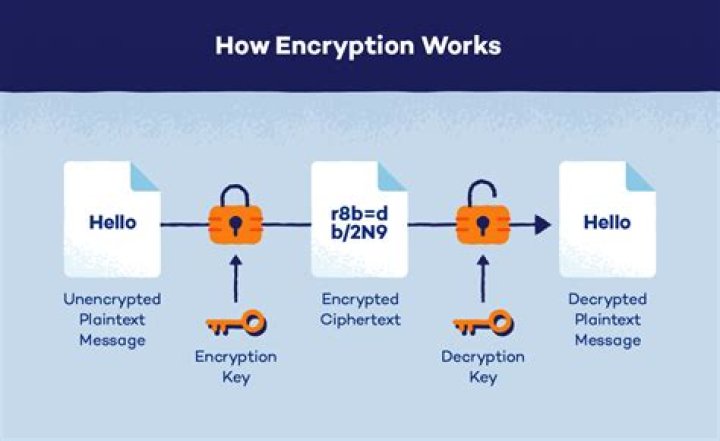
How do I unencrypt PGP?
- Open the e-mail containing the encrypted message in ciphertext.
- Highlight the block of ciphertext.
- Open the PGP Tray.
- Select Current Window. Choose Decrypt & Verify.
- Enter a passphrase into the PGP Enter Passphrase dialog box. Click OK.
- The decrypted message will come up in a new window for you to read.
Is PGP encryption secure?
Because the algorithm used by PGP – normally the RSA algorithm – is essentially unbreakable, PGP offers a highly secure way of encrypting files at rest, especially when used alongside a Threat Detection and Response Solution.Is it illegal to have a PGP?
It is probable (not certain, but probable) that PGP falls under the ITAR restrictions, which control the export of munitions and cryptographic technology from the US and Canada. If this is the case, it is illegal to export PGP from the USA or Canada to any other country.
Has AES 256 been broken?
The difference between cracking the AES-128 algorithm and AES-256 algorithm is considered minimal. … In the end, AES has never been cracked yet and is safe against any brute force attacks contrary to belief and arguments.
Can GPG be cracked?
If you have a GPG private key that is locked with a password, “cracking” the key reduces to password guessing. There’s a easy equation to answer that; what’s hard is that there are two unknowns: the number of bits of entropy in the password and the number of guesses per second at attacker can make.
Is PGP dead?
PGP is officially dead. Matrix is out of beta and working on making end-to-end encryption the default.Why is PGP bad?
PGP does a mediocre job of signing things, a relatively poor job of encrypting them with passwords, and a pretty bad job of encrypting them with public keys. PGP is not an especially good way to securely transfer a file. It’s a clunky way to sign packages. It’s not great at protecting backups.
What is better than PGP?Modern alternative: nacl/box and nacl/secretbox. These are general-purpose replacements for encrypting any kind of data. They support public-key and secret-key encryption, respectively, and both use secure modern modes and ciphers.
Article first time published onIs PGP encryption free?
It’s available as a free software download and is based on the Open PGP encryption standards established by the IETF. GPG is defined by RFC 4880 (the official name for the Open PGP standard).
Can you decrypt PGP with a public key?
You cannot decrypt with the public key, you must have the private key. That’s the asymmetric part of asymmetric cryptography.
Is PGP same as GPG?
GPG is a different implementation of the Open PGP standard and a strong alternative to Symantec’s official PGP software. GPG is defined by RFC 4880 (the official name for the Open PGP standard). … GPG can open and decrypt files encrypted by PGP or Open PGP, meaning it works well with other products.
What is the key size allowed in PGP?
10. What is the key size allowed in PGP? Explanation: Pretty good privacy security system allows 1024 to 4096 bits of key size.
Who invented PGP?
Original author(s)Phil Zimmermann PGP Inc. Network Associates PGP Corp.TypeEncryption softwareLicenseCommercial proprietary software
Does PGP encrypt data by using a block cipher called?
PGP encrypts data by using a block cipher called. … Private data encryption algorithm.
Where is GPG conf?
The default configuration files are ~/. gnupg/gpg. conf and ~/. gnupg/dirmngr.
How do I reset my GPG passphrase?
- open Keychain (not GPG Keychain Access)
- enter “GnuPG” in the search field.
- if you don’t see any entry your passphrase was not stored in the OS X keychain.
- otherwise double click that entry.
- click “Show Password” and verify with your admin password.
Does 512-bit encryption exist?
128-bit symmetric keys are considered to be roughly as strong as 1024-bit RSA keys, and 256-bit symmetric keys are considered to be roughly as strong as 2048-bit RSA keys. … There isn’t a single 512-bit symmetric key cipher in common public use.
Is AES hackable?
The attack used a known-key to discern the structure of the encryption. However, the hack only targeted an eight-round version of AES 128—not the standard 10-round version—so it would not be a major threat. Since the AES cipher itself is so secure, the main risk comes from side-channel attacks.
Can the NSA Break AES?
According to the Snowden documents, the NSA is doing research on whether a cryptographic attack based on tau statistic may help to break AES. At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented.
What replaced PGP?
GnuPG is another free encryption standard that companies may use that is based off of OpenPGP. GnuPG serves as a replacement for Symantec’s PGP.
Can NSA crack VPN?
VPNs can be hacked, but it’s hard to do so. … Existing VPN Vulnerabilities and ExploitationsEdward Snowden and other security researchers previously revealed that the US spy agency, the NSA, did crack the encryption protecting a large amount of internet traffic, including VPNs.
Does PGP have backdoor?
A backdoor is a “feature” in the software of PGP — in what I call the utility functions and not in the encryption algorithm — that allows an outside party to decrypt what you have encrypted. While the ADK feature is technically a backdoor, most attention is directed to the possibility of an unknown, hidden backdoor.
Does WhatsApp use PGP?
PGP for WhatsApp. Send messages over WhatsApp using PGP to add a second layer of End-to-End encryption. … PGP for WhatsApp is built using openpgp.
Does Gmail use PGP?
Gmail encryption: End-to-end encryption (An iOS app is also available in a pre-release testing form.) FlowCrypt adds a special “Encrypt and Send” button into your inbox interface, which allows you to send encrypted messages using the PGP (Pretty Good Privacy — yes, that’s actually what it’s called) standard.
Is PGP same as SSH?
SSH, PGP and SSL all use exactly the same RSA keypairs; with SSH, the keypairs are just stored “as is” – SSH is a no frills user of RSA. with PGP and SSL, the keys are usually embedded in a larger structured record along with a digital signature, some ownership information, and so forth.
Is PGP better than AES 256?
PGP is just as strong as that of AES, but it adds an additional layer of security to prevent anyone who only has the public key from being able to decrypt data. Another benefit of asymmetric encryption is that it allows for authentication.
Is AES better than PGP?
AES is fast and works best in closed systems and large databases; PGP should be used when sharing information across an open network, but it can be slower and works better for individual files.
Can PGP use AES?
PGP encryption is the standard when it comes to encrypting files that need to be transferred. … Also know that when encrypting a file with PGP, you may be using AES encryption. AES encryption and PGP encryption solutions work together to ensure that all your sensitive data is secure.
What encryption does Whatsapp use?
It uses Message Key which is generated by HMAC-SHA256 and Message Key is Protected by AES256 for end to end. So basically, they use SHA256 for Message key to be delivered to the client and these keys are responsible for decrypting messages (actual).