How do you do AWS penetration testing
Fill out penetration test request form.Tell AWS the dates that testing will take place.Tell AWS the IP Address range the scan or penetration testing will come from.Tell AWS the IP Address range being tested (scope)
Does AWS have penetration testing?
AWS customers are welcome to carry out security assessments or penetration tests against their AWS infrastructure without prior approval for 8 services, listed in the next section under “Permitted Services.” … Resellers of AWS services are responsible for their customer’s security testing activity.
How do you conduct AWS vulnerability scanning?
- Choose an AWS vulnerability scanner. Historically, AWS required express permission to run any form of vulnerability assessment on servers within the AWS infrastructure. …
- Run the scan to identify risks. …
- Analyze results and address vulnerabilities.
How do you perform a cloud penetration test?
- Step 1: Understand the cloud service provider’s policies. …
- Step 2: Create a cloud penetration testing plan. …
- Step 3: Execute the plan. …
- Step 4: Detect and fix vulnerabilities.
What are the steps of penetration testing?
- Information Gathering.
- Reconnaissance.
- Discovery and Scanning.
- Vulnerability Assessment.
- Exploitation.
- Final Analysis and Review.
- Utilize the Testing Results.
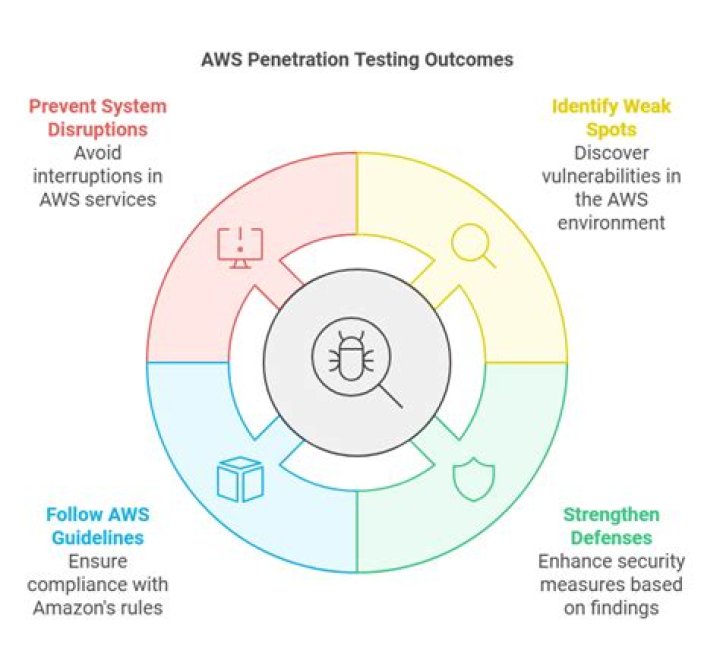
What is a cloud penetration test?
Cloud Penetration Testing is an authorised simulated cyber-attack against a system that is hosted on a Cloud provider, e.g. Amazon’s AWS or Microsoft’s Azure. The main goal of a cloud penetration test is to find the weaknesses and strengths of a system, so that its security posture can be accurately assessed.
Is penetration testing legal?
And is it illegal to do penetration testing in California? Pen testing is legal in all fifty US states, including California. Federal law covers the illegal aspect of hacking in the 1986 Computer Fraud and Abuse Act (CFAA).
What should be considered when Pentesting a cloud instance?
Another aspect to consider when planning a penetration test on a system within a cloud platform is whether pivoting is required. Pivoting is a common attack technique where a system is compromised to attack another system via that obtained access. This might, for instance, circumvent firewall filtering.What are the industry leading tools used for penetration testing?
- Powershell-Suite. The PowerShell-suite is a collection of PowerShell scripts that extract information about the handles, processes, DLLs, and many other aspects of Windows machines. …
- Zmap. …
- Xray. …
- SimplyEmail. …
- Wireshark. …
- Hashcat. …
- John the Ripper. …
- Hydra.
For example, you can start with a 10 node cluster and then easily increase to 50 nodes as your requirements change. Infrastructure Agility:Cloud allows companies to significantly decrease the time it takes to provision and de-provision IT infrastructure.
Article first time published onDoes AWS scan for vulnerabilities?
Amazon Inspector is an automated vulnerability management service that continually scans AWS workloads for software vulnerabilities and unintended network exposure.
How do I scan AWS environment?
- Make sure you meet the AWS scanning requirements.
- Submit your AWS regions for scanning by hitting the Add Scanning Target button in the Scanning\Scanning Targets section of the web console.
What is AWS xray?
AWS X-Ray is a service that helps developers analyze and debug distributed applications. Customers use X-Ray to monitor application traces, including the performance of calls to other downstream components or services, in either cloud-hosted applications or from their own machines during development.
What is penetration testing with example?
Penetration tests may include any of the following methods: Using social engineering techniques to access systems and related databases. Sending of phishing emails to access critical accounts. Using unencrypted passwords shared in the network to access sensitive databases.
What is the best preparation for a pen test?
- Identify and communicate your scope and objectives with the security professionals conducting your pen test. …
- Decide on the best time to conduct the test. …
- Backup your data. …
- Ensure that your internal IT team is available. …
- Explain what you want to see in the report.
What are the 4 phases of pen testing?
- Planning Phase. As you begin the penetration testing process, a practice lead will start by defining the scope of your security assessment. …
- Pre-Attack Phase. Before testing begins, the pre-attack phase is critical. …
- Attack Phase. …
- Post-Attack Phase.
How much does a penetration test cost?
Penetration testing can cost anywhere from $4,000-$100,000. On average, a high quality, professional pen test can cost from $10,000-$30,000. A lot of these costs are determined by factors such as: Size: A smaller, less complex organization is certainly going to cost less than that of a large company.
How much do penetration testers get paid?
As of May 2021, PayScale reports that the median annual penetration tester salary is around $86,000. A host of factors impact the salary, including education, experience, job type and job location. For example, penetration testers with 10 to 20 years of experience in the field can earn more than $120,000 yearly.
How long does a penetration test take?
A penetration test can take between one and three weeks to perform. The time it takes to complete a penetration test depends on the type of test, the type and number of systems being evaluated, and the strength of your existing cybersecurity.
What does AWS inspector do?
Amazon Inspector is an automated security assessment service that helps improve the security and compliance of applications deployed on AWS. Amazon Inspector automatically assesses applications for exposure, vulnerabilities, and deviations from best practices.
Which controls are managed by AWS?
- Inherited Controls – Controls which a customer fully inherits from AWS.
- Shared Controls – Controls which apply to both the infrastructure layer and customer layers, but in completely separate contexts or perspectives.
Can Nessus do penetration testing?
At Tenable, results from your Nessus scans can be integrated with popular penetration testing tools. This makes it even easier to start penetration testing from a solid foundation.
What is a Pentesting tool?
Penetration testing tools are software applications used to check for network security threats. Each application on this list provides unique benefits. Easy comparison helps you determine whether the software is the right choice for your business.
Is Nmap a penetration testing tool?
Nmap is a port scanner more than a penetration testing tool. But it aids pen testing by flagging the best areas to target in an attack. That is useful for ethical hackers in determining network weaknesses. And because it’s open source, it’s free.
What are biggest AWS security vulnerabilities?
- 1) Overuse of Public Subnets. Many organizations use the default Virtual Private Cloud (VPC) built into AWS, making few changes to the configuration. …
- 2) IAM Issues. …
- 3) Misconfigured S3 buckets. …
- 4) Exposed Database Origin Servers. …
- 5) Server-Side Request Forgery (SSRF) …
- 6) Hanging DNS Records.
What is an EC2 compute unit?
EC2 Compute Units represent the number of compute units allocated to each instance multiplied by the number of virtual cores, making it easier to compare capabilities of different Amazon EC2 Instance types.
What is AWS agility?
Agility is the practice of “building in” the ability to change quickly and inexpensively. … The cloud not only makes these other practices practical but provides agility on its own. Infrastructure can be provisioned in minutes instead of months, and de-provisioned or changed just as quickly.
What is elasticity in cloud computing?
What is elastic computing or cloud elasticity? Elastic computing is the ability to quickly expand or decrease computer processing, memory, and storage resources to meet changing demands without worrying about capacity planning and engineering for peak usage.
What is latency in cloud computing?
Cloud service latency is the delay between a client request and a cloud service provider’s response. Latency greatly affects how usable and enjoyable devices and communications are. … The customer network’s wide area network (WAN), if busy, can also have a significant effect on latency.
What is AWS CloudTrail?
AWS CloudTrail enables auditing, security monitoring, and operational troubleshooting by tracking user activity and API usage. CloudTrail logs, continuously monitors, and retains account activity related to actions across your AWS infrastructure, giving you control over storage, analysis, and remediation actions.
What is Cloud Mapper?
Cloud Drive Mapper integrates cloud storage into desktop computers and VDIs. It maps drive letters to OneDrive for Business, SharePoint Online, MS Teams and soon to Google Drive too.