How does auth0 authentication work
Integrate Auth0 in your Application.Setting Up the Application.Initialize the SDK.Evaluate the authentication state.Log In to the Application.Log the User Out.Read the User Profile.
How do you use Auth0 authentication?
- Integrate Auth0 in your Application.
- Setting Up the Application.
- Initialize the SDK.
- Evaluate the authentication state.
- Log In to the Application.
- Log the User Out.
- Read the User Profile.
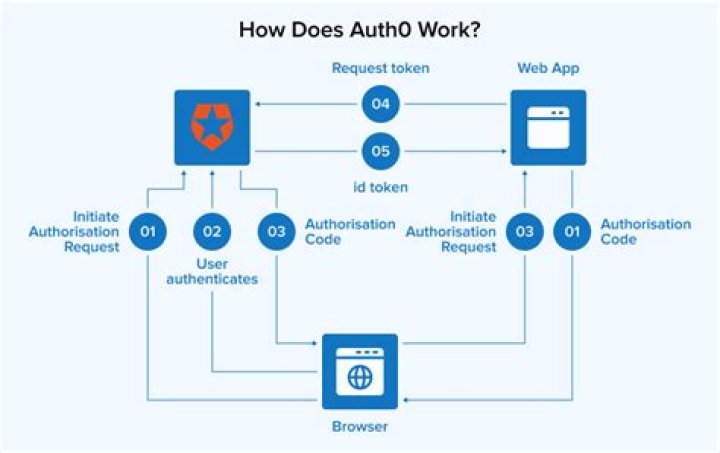
How does authentication process work?
The process is fairly simple; users input their credentials on the website’s login form. That information is then sent to the authentication server where the information is compared with all the user credentials on file. When a match is found, the system will authenticate users and grant them access to their accounts.
What is Auth0 and how does it work?
Auth0 is a flexible, drop-in solution to add authentication and authorization services to your applications. … You built a JavaScript front-end app and a mobile app, and you want them both to securely access your API. You have a web app that needs to authenticate users using Security Assertion Markup Language (SAML).How does authentication work in node?
- Step 1 – Create a directory and initialize npm. …
- Step 2 – Create files and directories. …
- Step 3 – Install dependencies. …
- Step 4 – Create a Node. …
- Step 5 – Create user model and route. …
- Step 6 – Implement register and login functionality.
What is Auth0 in API?
Introduction. The Authentication API enables you to manage all aspects of user identity when you use Auth0. It offers endpoints so your users can log in, sign up, log out, access APIs, and more. The API supports various identity protocols, like OpenID Connect , OAuth 2.0, and SAML .
Why is Auth0 so expensive?
Auth0’s main product is for managing public user access to your app. … Of course it can also just authenticate users, but that’s a tiny part of the functionality which is why it is so much more expensive.
How do authentication tokens work?
Token based authentication works by ensuring that each request to a server is accompanied by a signed token which the server verifies for authenticity and only then responds to the request.Can I use Auth0 for free?
Free plan. Get Auth0 for free with up to 7,000 active users and unlimited logins. No credit card required.
Is Auth0 safe?Auth0 has achieved a Level 2 audit Gold CSA Star certification for its cloud service security capabilities. Auth0 is compliant with the Payment Card Industry (PCI) Data Security Standard (DSS) that requires strict security controls and processes for transacting customer payment card data.
Article first time published onWhat is the best authentication method?
- Biometric Authentication. Biometric authentication relies on the unique biological traits of a user in order to verify their identity. …
- QR Code. QR code authentication is typically used for user authentication and transaction validation. …
- SMS OTP. …
- Push Notification. …
- Behavioral Authentication.
What are two steps involved in authentication process?
However, two-factor authentication processes involve the same general, multistep process: The user is prompted to log in by the application or the website. The user enters what they know — usually, username and password. Then, the site’s server finds a match and recognizes the user.
What are the three types of authentication?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
Is Auth0 good?
Critical Review It has been a great experience using the product, given that Auth0 is a trusted Identity product, we have not much complains benefiting from the features that the product is getting us.
What is the difference between Okta and Auth0?
Auth0 was designed primarily as an identity management platform for application builders. It provides simplicity and strong “identity management protocols.” Okta offers a more “complex” and more secure system.
How do I install Auth0?
- Log in to an existing WordPress site as an administrator.
- Go to Plugins > Add New in the admin menu on the left.
- Search for “Login by Auth0”
- For the Login by Auth0 plugin, click Install Now, then Activate.
How long is Auth0 free?
The trial period lasts 22 days. After that, the free plan gets activated automatically. If you wish to continue using some of the features from our Developer, Developer Pro or Enterprise plans, please choose one from above.
Is Auth0 Guardian free?
and start using Auth0 and Guardian for free!
Is Auth0 necessary?
Yes, if you are just a user… but if you are interested in developing applications, you need to find the most effective way to add authentication to your app. … We suggest using Auth0 for these purposes because this solution is both convenient and profitable.
How do I secure API using Auth0?
- An app authenticates a user with Auth0.
- Auth0 responds with the user’s ID Token and Access Token.
- The app calls your API, passing along the Access Token.
- Your API validates the Access Token.
- Your API responds with the requested information.
How do I create a Auth0 API?
- Go to Dashboard > Applications > APIs, and select + Create API.
- Make the implementation changes to your API that are described in the QuickStart. These changes consist of choosing a JWT library from a predefined list and configuring this library to validate the access tokens in your API.
How do you call Auth0 API?
- Configure your API. Once you have created your API, you will need to configure any scopes that applications can request during authorization.
- Get an Access Token. Your app requests an Access Token from your Auth0 Authorization Server using the Authorization Code Flow with PKCE.
- Call your API.
Is Auth0 an OAuth?
Auth0 uses the OpenID Connect (OIDC) Protocol and OAuth 2.0 Authorization Framework to authenticate users and get their authorization to access protected resources.
Is Auth0 open source?
Today, we are excited to announce the release of the Auth0 Open Source Single-Sign-On Dashboard.
How much does Auth0 enterprise cost?
UnitsDescription12 MONTHSEnterprise Subscription10,000 External Users, 5 Enterprise Connections, 1,000 API Calls / Mo$27,000Custom ConfigurationCustom Private Offers available [email protected]$27,000
How do I authenticate a token?
- Request: The person asks for access to a server or protected resource. …
- Verification: The server determines that the person should have access. …
- Tokens: The server communicates with the authentication device, like a ring, key, phone, or similar device.
How do I build an authentication system?
- Get the username and password from user.
- Set it in request form params and send it to the server.
- Server validates the user based on the given username and password
- Once successful validation, create a cookie and set it in the response.
- The client then uses this cookie/session to make future requests.
How do you test basic authentication in Postman?
To set up your test, go to the request in Postman that you need to authenticate and click on the Authorization tab. On that tab there is a Type dropdown where you can select the type of authorization your API uses. Select Basic Auth from there. This header is how your username and password are given to the server.
Is Auth0 a Fedramp?
— July 31, 2018 — Auth0, a global leader in Identity-as-a-Service (IDaaS), today announced it has achieved ISO 27001:2013 and ISO 27018:2014 certification, signifying Auth0’s ongoing commitment to providing its customers with the highest standards for information security.
What encryption does Auth0 use?
Auth0 helps you prevent critical identity data from falling into the wrong hands. We never store passwords in cleartext. Passwords are always hashed and salted using bcrypt. Additionally, data encryption is offered at rest and in transit by using TLS with at least 128-bit AES encryption.
Is local authentication safe?
Authenticating with Local Authentication is easier and has its benefit, but be wary of the risks. … Developers need to set up access control on the keychain so when users attempt to retrieve the secure item stored, they must authenticate with the device passcode (and therefore, Touch ID).