Is AES encryption symmetric or asymmetric
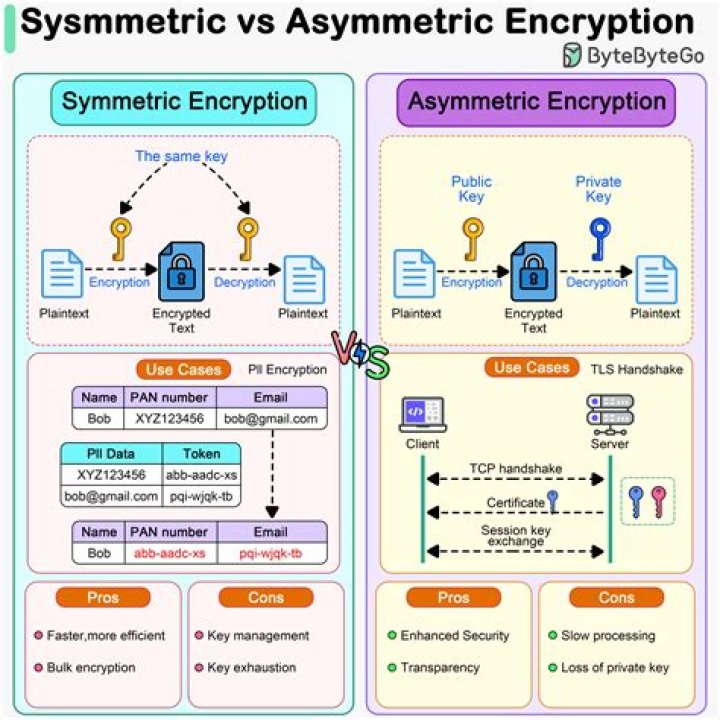
AES is a symmetric key cipher. This means the same secret key is used for both encryption and decryption, and both the sender and receiver of the data need a copy of the key. By contrast, asymmetric key systems use a different key for each of the two processes.
What type of encryption is AES?
AES encryption One of the most secure encryption types, Advanced Encryption Standard (AES) is used by governments and security organizations as well as everyday businesses for classified communications. AES uses “symmetric” key encryption. Someone on the receiving end of the data will need a key to decode it.
Which is better asymmetric or symmetric encryption?
Asymmetric encryption is the more secure one, while symmetric encryption is faster. They’re both very effective in different ways and, depending on the task at hand, either or both may be deployed alone or together. Only one key (symmetric key) is used, and the same key is used to encrypt and decrypt the message.
Is asymmetric encryption symmetric?
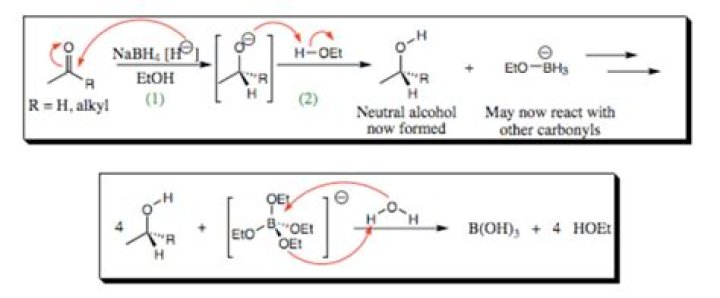
The basic difference between these two types of encryption is that symmetric encryption uses one key for both encryption and decryption, and the asymmetric encryption uses public key for encryption and a private key for decryption.Is cipher symmetric or asymmetric?
Symmetric Key EncryptionAsymmetric Key EncryptionThe encryption process is very fast.The encryption process is slow.
Which key is used in symmetric encryption?
What is Symmetric Encryption? Symmetric encryption is a type of encryption where only one key (a secret key) is used to both encrypt and decrypt electronic information.
Is RSA symmetric or asymmetric?
RSA is named for the MIT scientists (Rivest, Shamir, and Adleman) who first described it in 1977. It is an asymmetric algorithm that uses a publicly known key for encryption, but requires a different key, known only to the intended recipient, for decryption.
Which of the following is an example of symmetric encryption?
Blowfish, AES, RC4, DES, RC5, and RC6 are examples of symmetric encryption. The most widely used symmetric algorithm is AES-128, AES-192, and AES-256. The main disadvantage of the symmetric key encryption is that all parties involved have to exchange the key used to encrypt the data before they can decrypt it.Is AES symmetric?
AES is a symmetric encryption algorithm because it uses one key to encrypt and decrypt information, whereas its counterpart, asymmetric encryption, uses a public key and a private key. Okay, let’s break that down.
Which of the following is an example of asymmetric encryption?Examples of asymmetric encryption include: Rivest Shamir Adleman (RSA) the Digital Signature Standard (DSS), which incorporates the Digital Signature Algorithm (DSA) Elliptical Curve Cryptography (ECC)
Article first time published onIs BitLocker symmetric or asymmetric?
BitLocker is the most effective way to protect your information in case of theft. The encryption mechanism used with this protection feature is AES (Advanced Encryption Standard). AES is a symmetric-key algorithm which basically means that the same cryptographic key is used for both encryption and decryption.
Does https use symmetric encryption?
An HTTPS connection between a client and a server uses both symmetric and asymmetric encryption. Like the previous one, asymmetric encryption is first used to establish communication and exchange secrets, and then symmetric encryption is used for the rest of the communication.
What are the 2 types of data encryption?
There are two types of encryption in widespread use today: symmetric and asymmetric encryption.
Is Caesar cipher symmetric or asymmetric?
A symmetric encryption is any technique where the same key is used to both encrypt and decrypt the data. The Caesar Cipher is one of the simplest symmetric encryption techniques, and of course, one of the easiest to crack.
What is not a symmetric encryption algorithm?
What is NOT a symmetric encryption algorithm? Explanation: DES, CAST, and IDEA are all symmetric algorithms. RSA is an asymmetric algorithm.
What is symmetrical and asymmetrical network?
Asymmetric Network: An asymmetric network has multiple routes for incoming and outgoing network traffic. … Symmetric Network: A symmetric network has a single route for incoming and outgoing network traffic. As such traffic takes the same route when entering or the network.
What is difference between RSA and AES?
RSA is an asymmetric algorithm designed for public-key cryptography. AES is a symmetric algorithm designed for private-key cryptography. It’s faster than RSA but only works when both parties share a private key.
Is AES Elliptic Curve?
The implemented AES 128, 192 and 256 algorithms are specified in the “Advanced Encryption Standard (AES)” document, i.e. Federal Information Processing Standards (FIPS) Publication 197. … The GRECC core implements encryption and decryption for an elliptic curve based on 233-bit key and point lengths.
Where is AES encryption used?
Where is AES used? AES encryption is commonly used in a lot of ways, including wireless security, processor security, file encryption, and SSL/TLS.
How are AES keys shared?
AES is a symmetric algorithm, so it does not have public and private keys – only a shared secret. In the simplest form: AES is a symetric algorithm, it uses the same key for encryption and decryption.So tat whoever has the key can read your message.
Is public key encryption asymmetric?
Public-key cryptography, or asymmetric cryptography, is an encryption scheme that uses two mathematically related, but not identical, keys – a public key and a private key. Unlike symmetric key algorithms that rely on one key to both encrypt and decrypt, each key performs a unique function.
How do you perform asymmetric encryption?
Asymmetric encryption uses a mathematically related pair of keys for encryption and decryption: a public key and a private key. If the public key is used for encryption, then the related private key is used for decryption. If the private key is used for encryption, then the related public key is used for decryption.
Is ECC asymmetric?
ECC is an approach — a set of algorithms for key generation, encryption and decryption — to doing asymmetric cryptography.
Is DH symmetric or asymmetric?
DH is not a symmetric algorithm – it is an asymmetric algorithm used to establish a shared secret for a symmetric key algorithm.
Is RC4 asymmetric?
RC4 is a stream symmetric cipher. It operates by creating long keystream sequences and adding them to data bytes. RC4 encrypts data by adding it XOR byte by byte, one after the other, to keystream bytes. The whole RC4 algorithm is based on creating keystream bytes.
What is the example of asymmetric?
Asymmetry exists when the two halves of something don’t match or are unequal. The American flag is an example of asymmetry. If you understand symmetry, you’re on your way to understanding asymmetry.
Which of the following algorithm uses asymmetric encryption AES DES RC4 DSA?
Symmetric EncryptionAsymmetric EncryptionStandard symmetric encryption algorithms are RC4, AES, DES, 3DES, and QUAD.Standard asymmetric encryption algorithms are RSA, Diffie-Hellman, ECC, El Gamal, and DSA.
What are the three symmetric encryption schemes?
Key LengthBlock SizeIDEA128 bits64 bitsRC440 to 256 bitsStream cipher
What is symmetric and asymmetric encryption explain with example?
The plaintext is encrypted to ciphertext utilising symmetric encryption to make use of speed. Asymmetric encryption is used for keys exchange used for symmetric encryption. This ensures the security of asymmetric cryptography, making sure only the intended recipient can perform decryption.
Which of the following is another name for asymmetric encryption?
Asymmetric encryption, also known as public-key encryption, is a form of data encryption where the encryption key (also called the public key) and the corresponding decryption key (also called the private key) are different.
Does BitLocker use AES?
BitLocker uses Advanced Encryption Standard (AES) as its encryption algorithm with configurable key lengths of 128 or 256 bits.