What is command and control malware
A command-and-control [C&C] server is a computer controlled by an attacker or cybercriminal which is used to send commands to systems compromised by malware and receive stolen data from a target network. … It can be used to disseminate commands that can steal data, spread malware, disrupt web services, and more.
What are command and control attacks?
A Command and Control attack is a component of a malware attack used to establish a remote covert channel between a compromised host and the attacker’s server. The attacker’s server is often referred to as a Command and Control server, C2 server, or C & C server.
What is command and control C2 malware?
The malware command and control (also called C&C or C2) refers to how attackers communicate and exhibit control of the infected system. … Today, the most common protocol used by the malware for the C2 communication is HTTP/HTTPS.
What is command and control when we are talking in terms of malware?
One popular method used by attackers to distribute and control malware is “command and control,” which is also called C2 or C&C. This is when bad actors use a central server to covertly distribute malware to people’s machines, execute commands to the malicious program, and take control of a device.What is botnet command and control?
“Command and Control” (C&C) servers are centralized machines that are able to send commands and receive outputs of machines part of a botnet. … Star topology botnets rely on one central C&C server, which sends commands to every bot in the botnet.
What is crypto malware?
Crypto-malware is a form of malware that enables a threat actor to carry out cryptojacking activity. While the process used by hackers is essentially the same as compared to that used by legitimate cryptominers, crypto-malware leverages another user’s devices and processing power to gain payment.
What are some of the problems with command and control?
Although such regulations have helped to protect the environment, they have three shortcomings: they provide no incentive for going beyond the limits they set; they offer limited flexibility on where and how to reduce pollution; and they often have politically-motivated loopholes.
What is C2 IP address?
One of the most common forms of indicator seen describes a pattern for TCP traffic beaconing to a specific command and control (C2, C&C) server. This idiom describes creating such an indicator in STIX.What is command and control leadership?
A command and control approach to leadership is authoritative in nature and uses a top-down approach, which fits well in bureaucratic organizations in which privilege and power are vested in senior management. It is founded on, and emphasizes a distinction between, executives on the one hand and workers on the other.
What are rootkits used for?A rootkit allows someone to maintain command and control over a computer without the computer user/owner knowing about it. Once a rootkit has been installed, the controller of the rootkit has the ability to remotely execute files and change system configurations on the host machine.
Article first time published onWhat is command and control callback?
A command-and-control [C&C] server is a computer controlled by an attacker or cybercriminal which is used to send commands to systems compromised by malware and receive stolen data from a target network. … C&C servers also serve as the headquarters for compromised machines in a botnet.
How do you find command and control?
You can detect C&C traffic in your log sources by using threat intelligence that is either produced by your own team or that you receive via threat sharing groups. This intelligence will contain, among other information, the indicators and patterns that you should look for in the logs.
How do I remove botnet malware?
- Power off the phone and reboot in safe mode. Press the power button to access the Power Off options. …
- Uninstall the suspicious app. …
- Look for other apps you think may be infected. …
- Install a robust mobile security app on your phone.
Who controls a botnet?
A botnet (short for “robot network”) is a network of computers infected by malware that are under the control of a single attacking party, known as the “bot-herder.” Each individual machine under the control of the bot-herder is known as a bot.
What is the difference between Command & control?
Command: The exercise of authority based upon certain knowledge to attain an objective. Control: The process of verifying and correcting activity such that the objective or goal of command is accomplished.
Why is command and control important?
In short, command and control is essential to all military operations and activities. With command and control, the countless activities a military force must perform gain purpose and direction. … Command and control is a fundamental requirement for life and growth, survival, and success for any system.
What are examples of command and control?
Command-and-control approach and environment standards It is a mandated level of performance enforced through a piece of legislation. A few examples are the limits set on the volume of timber that could be harvested, bans on the cutting of trees, and maximum levels legally allowed for pollution emissions.
Is crypto malware a ransomware?
These days, however, there is an entire new generation of malware called crypto-malware. This is ransomware that encrypts all of the data on your computer and holds that data for ransom. It’s going to encrypt all of your data files.
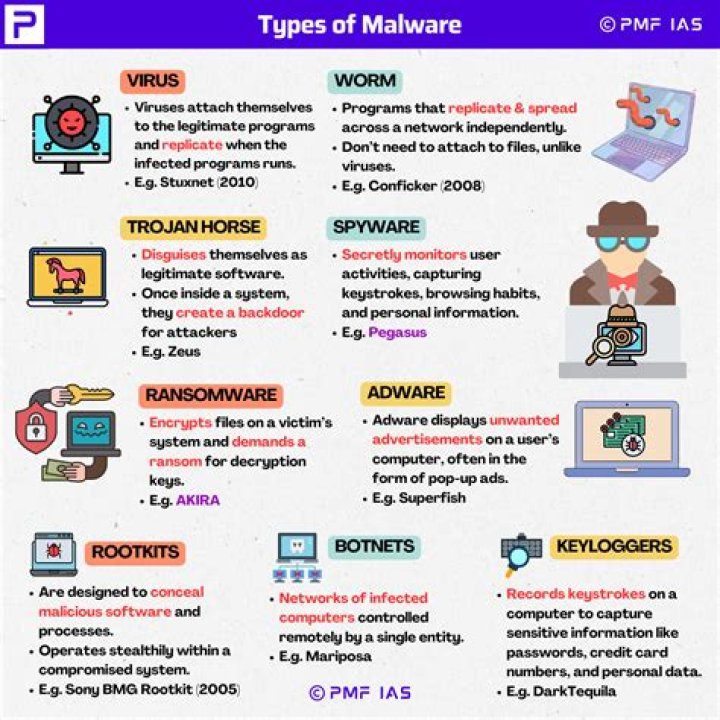
Is rootkit crypto malware?
The rootkit component of the cryptocurrency-mining malware is a slightly modified/repurposed version of a publicly available code. Upon installation, all processes named “ kworkerds ” will be invisible to process monitoring tools.
What is a crypto file?
A CRYPTO file is an encrypted file created by MacPaw Encrypto encryption software to securely store data. … CRYPTO files are created to protect files or folders that contain sensitive information.
Is commanding and leading the same?
As adjectives the difference between commanding and leading is that commanding is tending to give commands, authoritarian while leading is providing guidance or direction.
What are the basic elements of command and control?
The elements of command are authority, responsibility, decision making, and leadership. The elements of control are direction, feedback, information, and communication.
What is the difference between mission command and command and control?
To get mission command right, leaders must first understand the difference between mission command and command and control. Commanders who lead through command and control make every decision for their organization. … Conversely, mission command relies on the art of leadership.
What is cobalt strike beacon?
Beacon is Cobalt Strike’s payload to model an advanced actor. Beacon executes PowerShell scripts, logs keystrokes, takes screenshots, downloads files, and spawns other payloads.
Which type of malware disables protection software?
1. Ransomware. Ransomware is software that uses encryption to disable a target’s access to its data until a ransom is paid.
What is cobalt strike and what is it used for?
Cobalt Strike is a commercial, full-featured, remote access tool that bills itself as “adversary simulation software designed to execute targeted attacks and emulate the post-exploitation actions of advanced threat actors“.
Is a Trojan a rootkit?
Rootkit is set of malicious program that enables administrator-level access to a computer network. … Trojan Horse is a form of malware that capture some important information about a computer system or a computer network.
What is Trojan Horse computer?
What Is a Trojan Horse Virus? A Trojan Horse Virus is a type of malware that downloads onto a computer disguised as a legitimate program. The delivery method typically sees an attacker use social engineering to hide malicious code within legitimate software to try and gain users’ system access with their software.
Can Malwarebytes detect rootkits?
Malwarebytes security software can scan and detect rootkits. Download Malwarebytes to your device and scan to see if any rootkits are detected. If so, click ok to remove them from your device.
What is a malware callback?
Malware callbacks normally come from the internal network to external hosts. The malware binary instructs the infected machine to transmit network callback traffic to the C&C host to signal the attacker that it is ready to be controlled remotely. … This scan can be considered a callback.
How does malware communicate?
Simple malware communicates using an Internet Relay Channel. … Once the communications channel is established, the command-and-control server will instruct the malware to download additional rootkits and remote access tools on the compromised host.