What is the point of hashing passwords
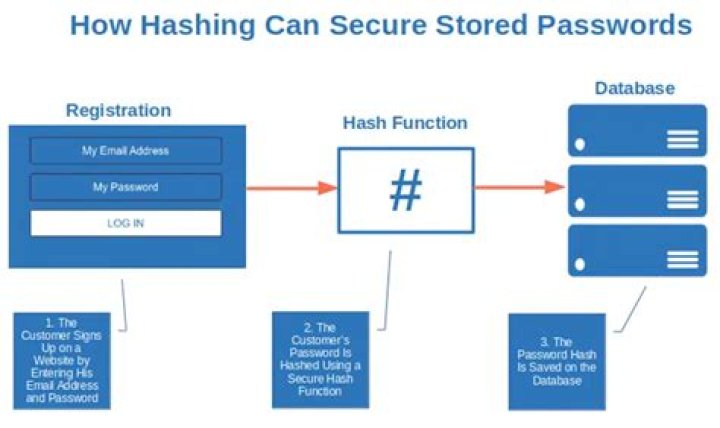
Hashing a password is good because it is quick and it is easy to store. Instead of storing the user’s password as plain text, which is open for anyone to read, it is stored as a hash which is impossible for a human to read.
What is the purpose of hashing a password?
Hashing performs a one-way transformation on a password, turning the password into another String, called the hashed password. “One-way” means that it is practically impossible to go the other way – to turn the hashed password back into the original password.
What can a hacker do with a hashed password?
So hashes of passwords can be used to confirm guesses at the real passwords. Depending on the fine details of how the password is hashed and the hardware available to the attacker, the attacker may be able to make many millions of guesses per second[2] against a password hash.
Why is it a good idea to hash passwords that are stored in a file?
Why is it a good idea to hash passwords that are stored in a file? Answer : It’s more secure to store hashed passwords because they are compared to y, and if y = h(x) then the entered password is assumed to be correct and the user is authenticated .What is the main purpose of using hash function?
Hash functions are used for data integrity and often in combination with digital signatures. With a good hash function, even a 1-bit change in a message will produce a different hash (on average, half of the bits change). With digital signatures, a message is hashed and then the hash itself is signed.
Why does a hash function used for message authentication need to be secured?
In accordance with FIPS 180-4, the hash algorithms are called secure because, for a given algorithm, it is computationally infeasible (1) to find a message that corresponds to a given message digest, or (2) to find two different messages that produce the same message digest.
What are the benefits of hashing?
- Hashing gives a more secure and adjustable method of retrieving data compared to any other data structure. It is quicker than searching for lists and arrays. …
- Hashed passwords cannot be modified, stolen, or jeopardized. …
- Two files can be compared for equality easily through hashing.
Why are hash values salted?
Recap. A cryptographic salt is made up of random bits added to each password instance before its hashing. Salts create unique passwords even in the instance of two users choosing the same passwords. Salts help us mitigate hash table attacks by forcing attackers to re-compute them using the salts for each user.Is hashing more secure than encryption?
Hashing and encryption both provide ways to keep sensitive data safe. However, in almost all circumstances, passwords should be hashed, NOT encrypted. Hashing is a one-way function (i.e., it is impossible to “decrypt” a hash and obtain the original plaintext value). … Hashing their address would result in a garbled mess.
How do hashes work?A hash function is a mathematical function that converts an input value into a compressed numerical value – a hash or hash value. Basically, it’s a processing unit that takes in data of arbitrary length and gives you the output of a fixed length – the hash value.
Article first time published onCan hashed passwords be recovered?
You can’t recover a hashed password – that’s the whole point! And you should NEVER email a password anyway! Give the user a password reset link.
Can a hashed password be cracked?
Not all hashing is created equal. … Some hashing schemes are more easily cracked than others. When hackers compromise a company to access its collection of users’ passwords, what they find and steal isn’t stored in a form that’s readable by humans—at least if the company has even a pretense of security.
Is a hashed password secure?
Whereas the transmission of the password should be encrypted, the password hash doesn’t need to be encrypted at rest. When properly implemented, password hashing is cryptographically secure.
Does hashing keep contents of messages confidential?
Whereas encryption algorithms are reversible (with the key) and built to provide confidentiality (some newer ones also providing authenticity), hashing algorithms are irreversible and built to provide integrity in order to certify that a particular piece of data has not been modified.
How hash functions are used for checking the integrity?
Verifying a Hash Data can be compared to a hash value to determine its integrity. Usually, data is hashed at a certain time and the hash value is protected in some way. At a later time, the data can be hashed again and compared to the protected value. If the hash values match, the data has not been altered.
Why hashing is used in data structure?
Hashing allows to update and retrieve any data entry in a constant time O(1). Constant time O(1) means the operation does not depend on the size of the data. Hashing is used with a database to enable items to be retrieved more quickly. It is used in the encryption and decryption of digital signatures.
Is hashing important for competitive programming?
Hashing algorithms are helpful in solving a lot of problems. We want to solve the problem of comparing strings efficiently. The brute force way of doing so is just to compare the letters of both strings, which has a time complexity of O(min(n1,n2)) if n1 and n2 are the sizes of the two strings.
Why is hash more efficient?
A primary impact of hash tables is their constant time complexity of O(1), meaning that they scale very well when used in algorithms. Searching over a data structure such as an array presents a linear time complexity of O(n). … Simply put, using a hash table is faster than searching through an array.
Is MAC a hash?
Security. While MAC functions are similar to cryptographic hash functions, they possess different security requirements. … In contrast, a digital signature is generated using the private key of a key pair, which is public-key cryptography.
What is difference between hash and MAC?
The main difference is conceptual: while hashes are used to guarantee the integrity of data, a MAC guarantees integrity AND authentication.
Can hashing identify duplicate files?
This function rapidly compares large numbers of files for identical content by computing the MD5 hash of each file and detecting duplicates. … Thus, since hashes rather than file contents are compared, the process of detecting duplicates is greatly accelerated.
What is the most secure hash algorithm?
Probably the one most commonly used is SHA-256, which the National Institute of Standards and Technology (NIST) recommends using instead of MD5 or SHA-1. The SHA-256 algorithm returns hash value of 256-bits, or 64 hexadecimal digits.
Can a hash be decrypted?
The principle of hashing is not to be reversible, there is no decryption algorithm, that’s why it is used for storing passwords: it is stored encrypted and not unhashable. … Hash functions are created to not be decrypted, their algorithms are public. The only way to decrypt a hash is to know the input data.
What is true about hashing?
Answer: Hashing is the transformation of a string of characters into a usually shorter fixed-length value or key that represents the original string. Hashing is used to index and retrieve items in a database because it is faster to find the item using the shorter hashed key than to find it using the original value.
Should I hash password before sending to server?
It should be irreversibly hashed before leaving the client as there is no need for the server to know the actual password. Hashing then transmitting solves security issues for lazy users that use the same password in multiple locations (I know I do).
What is a hash clash?
In computer science, a collision or clash is a situation that occurs when two distinct pieces of data have the same hash value, checksum, fingerprint, or cryptographic digest.
Why are hashes irreversible?
2 Answers. It is irreversible in the sense that for each input you have exactly one output, but not the other way around. There are multiple inputs that yields the same output. For any given input, there’s a lot (infinite in fact) different inputs that would yield the same hash.
What happens on a hash run?
A hash blends running with orienteering as groups of “hounds” chase a chalk “hare” across city and country, treading the previous weekend’s excesses into the pavement. … These are either predetermined or marked on the fly by the lead runners (hares), while the rest of the group (hounds) follow.
How is hashing used in Blockchain?
Blockchain Hash Function. A hash function takes an input string (numbers, alphabets, media files) of any length and transforms it into a fixed length. … The fixed-length output is called a hash. This hash is also the cryptographic byproduct of a hash algorithm.
What will happen if a hacker enters a stolen hash into a password field?
So when the user logs in next time, they enter their password, which is sent over the network. … It’s not possible to simply undo the hashing to recover the original password. Even if the database is stolen, the attackers only have the hashed passwords, rather than the passwords themselves.
Can you brute force a hashed password?
An attacker with access to the password hashes can do a brute-force attack on them, by guessing each password from a dictionary. To prevent this, verification of passwords should be relatively slow.

